In recent years, interest has been growing considerably regarding the impact of the forthcoming E-mobility ecosystem on power system operations. In the recent report of ETIP SNET [1], the E-mobility deployment and the impact on grids is discussed in detail. The growing number of electric vehicles that will interact with the grid in the coming years will certainly require special attention from grid operators. Electric vehicles could represent a load, a large-scale energy storage system and a flexible distribution resource for grid services. In order to take advantage of all the potential opportunities and potential challenges that the E-mobility ecosystem can bring, optimal management of the bi-directional charging process will be critical.
Managing and monitoring of the charging process through the appropriate communication and control systems allowing real time control will enable grid operators to unlock the opportunities to the system. Opportunities such as, reshaping the power load curve, ancillary services for system operation, management of grid congestion, avoid overloads on distribution grids, voltage control in distribution grids, reduction of overgeneration by RES, behind the meter services, advantages of Hyper chargers for Heavy Duty Vehicles, are also challenges of the near future.
Furthermore, over the last years, significant research has been conducted on how potential malicious control of EV charging stations and general EV system equipment could lead to power system maloperation [2]. Even though most of the research findings indicate a more significant impact on the distribution network, the transmission network can be affected as well, in various ways. A possible energy market manipulation cyberattack that leverages high wattage IoT botnets, can generate an event that could slightly change the total demand of the power grid with the aim of affecting the electricity prices in the favor of specific market players [3].
Sudden load changes in the demand side that can be caused by EV botnets cyberattack, can also cause frequency issues to the system. Although generators are protected from high and low frequency values by protective relays, sudden increase or decrease in the load buses, cause the system’s frequency to go below or above the frequency cut-off limits. Of course, someone would argue that the drop or rise in frequency will be higher only in a low inertia system. This suggests that an attack that is not effective today, may be effective tomorrow if the system’s inertia is lower due to a higher rate of RES penetration [4-5].
Regarding the EV charging stations, in [6] it is argued that possible subversion or malicious endpoints in the OCPP protocol can also lead to destabilization of power networks. Energy theft or fraud cyber attacks that, interfere with resource reservation originating with the EVs, may also be initiated by a man in the middle attack. Such attacks, which could be widely replicated, would result in excessive or insufficient provisioning of power supply or even the total or partial disintegration of the resilience and stability of power grids.
It is widely believed that EVs are the key enablers for a sustainable society, by allowing renewables to further penetrate in our energy mix, and significantly reducing the carbon footprint of land transportation. As EVs are rapidly adopted across Europe, new cybersecurity concerns are raised, since EV charging stations can be leveraged by cyber attackers to cause cascading effects against residential/commercial areas and Critical Infrastructures.
In that sense, the impact of an E-Mobility ecosystem in the TSO level, is crucial and the participation of IPTO in Use Case 2 of the ELECTRON project, raises the awareness and addresses the future challenges that the network operator will face.
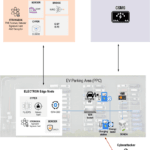
This Use Case from one hand, deals with cyber-attacks against Electric Vehicle (EV) charging stations, and from the other hand, cyberattacks against the RTUs of a TSO substation. Various cyber-attacks will be unleashed to validate the ELECTRON platform’s ability to protect the EV charging infrastructure. A network of EV chargers is functional due to the proper operation of a complex EPES network, consisting of power generation systems, transmission systems, and distribution to end users. It is expected that any significant anomaly or cyberattack across the energy chain may affect the EV charging network. For example, a cyberattack against the RTUs of a TSO substation may affect the power supply of the underlying DSO substations, thus, the attached EVCSs as well. Moreover, it is remarkable that threats with similarities can be found across the energy chain. IPTO will contribute to this use case scenario to demonstrate how data from TSO and CPO infrastructure can be combined, utilizing federated learning, to boost the detection performance on both EPES domains.
[1]. European Commission, Directorate-General for Energy, Gallego Amores, S., E-mobility deployment and impact on grids – Impact of EV and charging infrastructure on European T&D grids : innovation needs, Gallego Amores, S.(editor), Publications Office of the European Union, 2022, https://data.europa.eu/doi/10.2833/937755.
[2]. Johnson, J.; Berg, T.; Anderson, B.; Wright, B. Review of Electric Vehicle Charger Cybersecurity Vulnerabilities, Potential Impacts, and Defenses. Energies 2022, 15, 3931. https://doi.org/10.3390/en15113931.
[3]. Rohde, K. Cyber Security of DC Fast Charging: Potential Impacts to the Electric Grid. In Proceedings of the S4x19, Miami, FL, USA, 14–17 January 2019.
[4]. Soltan, S.; Mittal, P.; Poor, H.V. BlackIoT: IoT Botnet of High Wattage Devices Can Disrupt the Power Grid. In Proceedings of the 27th USENIX Security Symposium (USENIX Security 18), Baltimore, MD, USA, 15–17 August 2018; pp. 15–32.
[5]. Khan, O.G.M.; El-Saadany, E.; Youssef, A.; Shaaban, M. Impact of Electric Vehicles Botnets on the Power Grid. In Proceedings of the 2019 IEEE Electrical Power and Energy Conference (EPEC), Montreal, QC, Canada, 16–18 October 2019.
[6]. Alcaraz, C.; Lopez, J.; Wolthusen, S. OCPP Protocol: Security Threats and Challenges. IEEE Trans. Smart Grid 2017, 8, 2452–2459.