A novel Cyber Hygiene methodology and ontology for EPES personnel is introduced, as proposed in ELECTRON Task 6.1. By leveraging a robust cybersecurity training framework tailored for critical infrastructures, we’ve incorporated these key components: (1) Training development model and learning model selection; (2) Training content; (3) Training delivery methods; and (4) Assessment and evaluation.
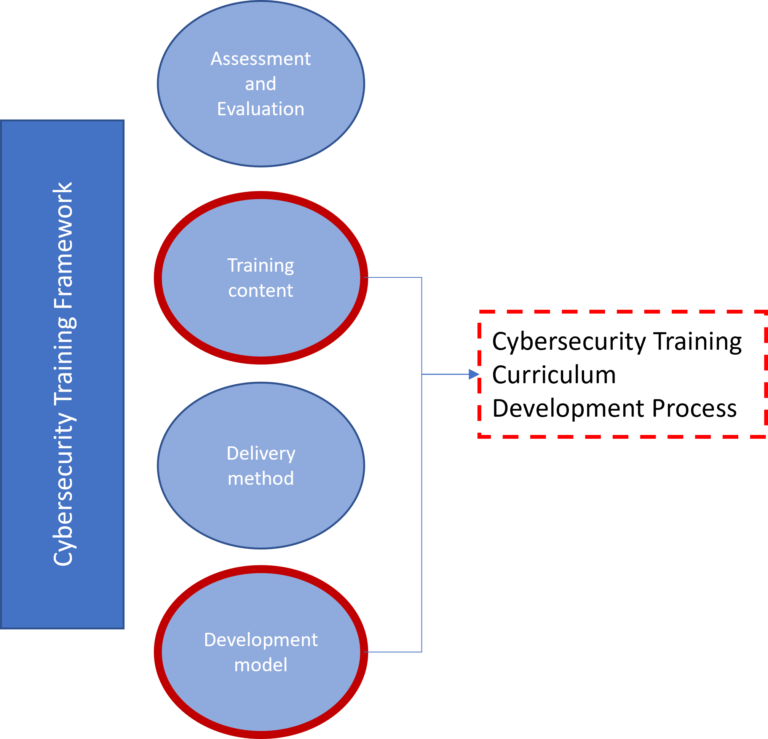
The primary goal is to craft a Cyber Hygiene methodology and ontology that sets new standards in cybersecurity. The development model is based on the analysis, design, develop, implement, and evaluate model and particularly incorporates the analysis, design, development, implementation, and evaluation phases. In the analysis phase the training needs, goals, outcomes, and learning environment are identified. During the design phase, the training content and the training structure are specified while in the development phase, the action plan, resources, and pilot test are developed. By leveraging the aforementioned outcomes, the organization and monitoring of the training program are performed in the implementation phase. Finally, the evaluation phase incorporates all the necessary formative and summative evaluations of the training cycle. To achieve the primary goal of the Cyber Hygiene, we’ve put components (1) and (2) to work in designing the Cyber Hygiene Training Curriculum. Particularly, the process focused on the Development and Training content phases of the methodology as it is depicted in Figure below. This curriculum increases the cybersecurity posture to defend against the most critical threats in power grids. The outcome of Task 6.1, especially the Cyber Hygiene Training Curriculum, is a significant step toward realizing the WP6 objective: designing an energy personnel training and certification platform for cybersecurity. Moreover, a set of technical and organisational best practices are included in the training curriculum towards increasing the security posture of EPES personnel. The Cyber Hygiene Training Curriculum took into consideration the involved actors, and entities, and use case descriptions to provide a comprehensive set of cybersecurity best practices against the most critical threats in a power grid. Further a Cyber Hygiene Ontology that complements the developed training curriculum is proposed. This ontology simplifies the analysis and communication of the Cyber Hygiene Training Curriculum for EPES personnel, offering the essential entities and relationships that describe this cybersecurity training.